●Data can become more free
Nishimura: First, please tell us about ZenmuTech Inc.'s mission and vision.
Abe: Our mission is to leverage secret sharing technology to thoroughly pursue both data protection and utilization. Until now, the focus has been more on "how to protect data" than "how to utilize it," with strict rules and constraints taking precedence. However, we aim for a society where data can be used more freely and effectively, unbound by those constraints.The message we want to convey is that "data can be much freer." Data undoubtedly has vast untapped potential. Yet corporate data is often heavily restricted and cannot leave the company. As a result, valuable information remains dormant, like raw gems. We want to break down these barriers with our technology and maximize the possibilities of data.
EN: Secret Sharing Technology that Distributes Data Fragments
Nishimura: Thank you. Now, please explain the mechanism of the secret sharing technology " EN."
Abe: Our mission is to leverage secret sharing technology to thoroughly pursue both data protection and utilization. Until now, the focus has been more on "how to protect data" than "how to utilize it," with strict rules and constraints taking precedence. However, we aim for a society where data can be used more freely and effectively, unbound by those constraints.The message we want to convey is that "data can be much freer." Data undoubtedly has vast untapped potential. Yet corporate data is often heavily restricted and cannot leave the company. As a result, valuable information remains dormant, like raw gems. We want to break down these barriers with our technology and maximize the possibilities of data.
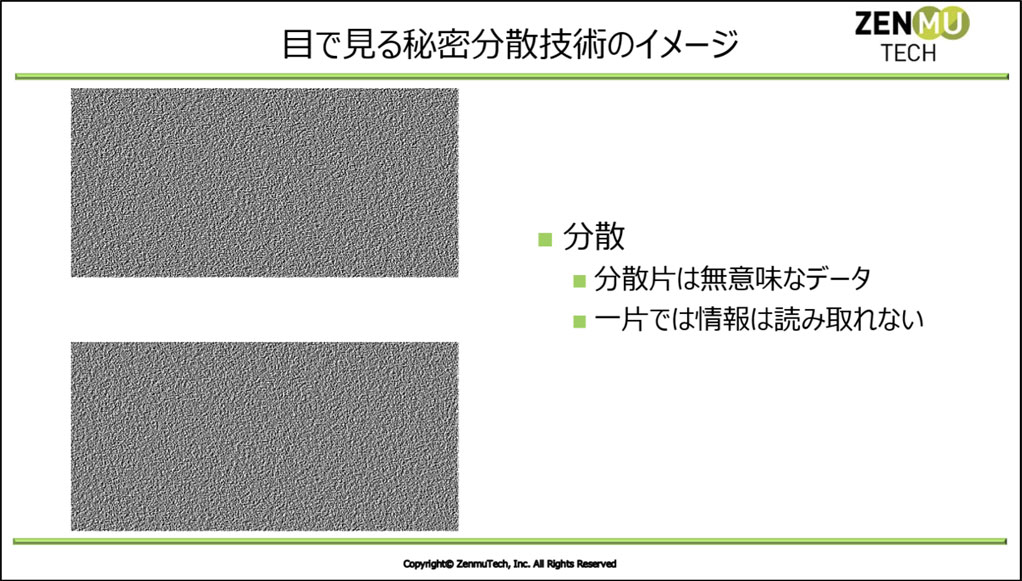
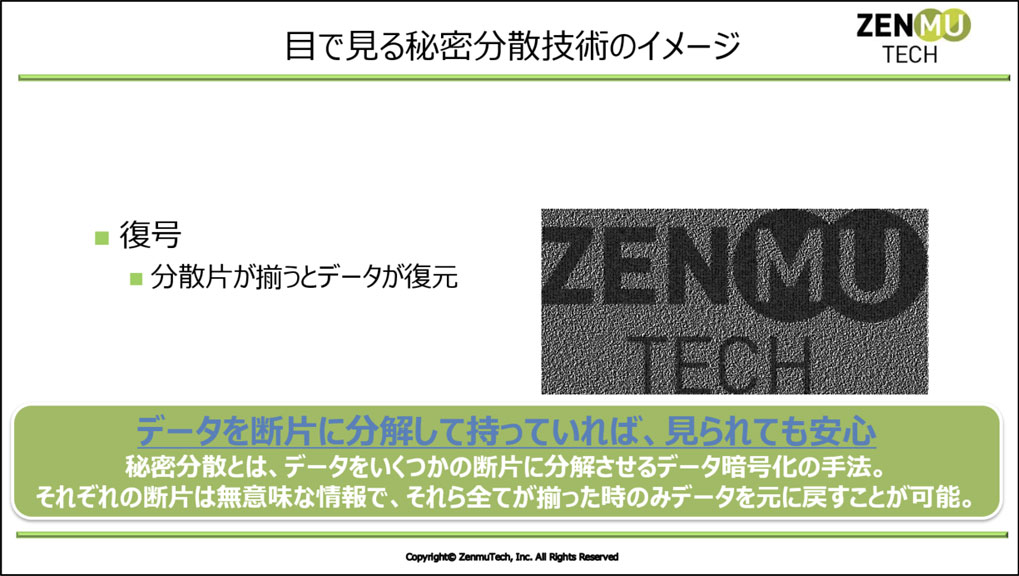
This mechanism is the concept of AONT (All-Or-Nothing Transform), the core idea behind secret sharing technology. By fragmenting and storing data, even if some fragments leak externally, they are meaningless individually, ensuring information security. Thus, secret sharing technology is one method that enhances security by decomposing data into multiple fragments and encrypting each one.
The concept of secret sharing has existed since ancient times and can be seen in Japanese history.For example, the "wooden seal" (kigui) used to seal checkpoints upon the Emperor's death involved splitting a single wooden tablet into two pieces, each stored in a different location. A messenger carried one piece, and the checkpoint administrator verified its authenticity by matching it with the other piece, thereby enforcing the seal. This concept of "meaningless individually, but effective only when combined" aligns with the principle of secret sharing. EN is a technology that applies the techniques used in these wooden seals to the modern digital environment.
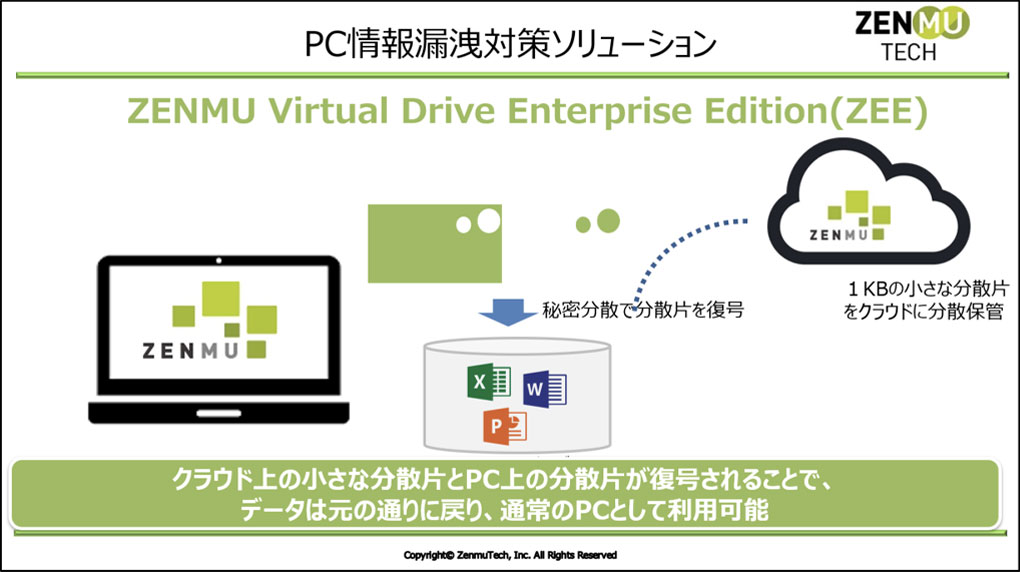
Let's explain how this applies to a PC. The user's data is secret-shared, with one part stored on the PC while the other is saved in the cloud. In this state, the data appears normal on the PC. However, the moment one fragment moves to the cloud and becomes separated from the PC, the data becomes invisible.This means that even if the PC is lost, information leakage does not occur. This is because the complete data does not exist on the PC; only the distributed fragments remain. When the PC reconnects to the network and reunites with the fragments in the cloud, the data is restored to its original form and becomes viewable again on the PC.
In this way, EN is a groundbreaking technology that changes the concept of "carrying data with you" and significantly reduces the risk of information leaks through an approach that differs from conventional encryption.
Nishimura: With the rapid spread of remote work, it seems the use of this service has also exploded. What is the actual user base size?
Abe: We have now surpassed 100,000 users overall.
● The strength of not relying on "keys"
Nishimura: Compared to general encryption technologies, could you tell us about EN features and advantages?
Abe: Conventional encryption technology protects data using keys. However, the problem is that if this key is compromised, the encrypted data can be easily decrypted. Typically, the key is replaced with a password managed by the user. Yet, the risks of password reuse, leakage, and cracking are ever-present.Even if less common now, some people still jot down passwords on sticky notes beside their PC screens. For large corporations, it's practically impossible to fully control how tens of thousands of employees each manage their passwords. Thus, encryption technology has a weakness: its reliance on a "key" concentrates risk at a single point.
In contrast, EN secret sharing EN divides data into multiple fragments for storage. Data cannot be restored unless all fragments are present. Its key advantage is dramatically enhanced security, achieved by not relying on a "key" like encryption does.
Furthermore, secret sharing allows for regular updates to the data distribution process. While conventional password management typically EN rules like "change every three months," EN updates data distribution EN frequently. Even if someone attempts to decrypt it, the fragments themselves cannot be used to infer the data. We take pride in this aspect as well, boasting higher security compared to traditional encryption technologies.
Nishimura: I see. I understand you've achieved very high security. However, doesn't that also mean the cost is high? What is the pricing structure per PC?
Abe: We offer it for 1,800 yen per virtual drive per month.
Nishimura: That's quite reasonable. It offers higher security than encryption, spreads the risk, and yet remains relatively affordable—it's no wonder users are increasing.
Nishimura: Please tell me about your current product lineup.
Abe: We have three main product lines. First, ZVD ( EN Virtual Drive). This is a product for securely protecting PC data. EN Engine. This provides secret sharing technology as a library, essentially an OEM business.By licensing it, other companies can integrate secret sharing technology into their own products and systems. Finally, there's secure computation. This technology enables computation while maintaining confidentiality by processing data in a distributed manner without encryption. Its key feature is the ability to utilize data while protecting it, making it another crucial product. These three form our current main product lineup.

●Significantly contributes to reducing the risk of information leaks
Nishimura: Could you tell me about the industries or applications where your company's technology is considered particularly effective?
Abe: Our services are utilized by a wide range of customers, regardless of company size or industry.While large corporations are certainly users, we've recently seen increasing demand from individual customers, such as freelancers, who want to "safeguard their PC data securely." Therefore, our services are not limited to specific industries. However, adoption is particularly advanced in the financial sector. The financial industry has historically been a heavy user of virtual desktops (VDI). When considering the costs and investments required to further expand existing environments, more cases are EN as a more flexible and secure solution. Consequently, there is a tendency for financial industry customers to be relatively numerous.However, this is purely about adoption history; it can be utilized in any industry, including manufacturing. We believe the benefits of implementation are substantial regardless of industry, especially for companies where employees carry PCs for work, as it significantly contributes to reducing the risk of information leaks.
Nishimura: Regarding the ZVD we discussed earlier, you mentioned it can be utilized anywhere by companies that carry PCs. For the EN Engine, what industries or companies would find it particularly effective?
Abe: This technology has broad applications. For example, it can prevent the resale of electronic tickets. By managing tickets as distributed fragments and only validating them when both parts match at the venue, fraudulent use can be prevented. Another area of particular interest is the drone sector.Critical corporate information (flight routes, imaging data, formation data, etc.) risks leakage through crashes or hacking. By secretly distributing this data, even if parts are stolen, the complete information cannot be disclosed. It is also effective for protecting surveillance camera footage. Video containing confidential information, such as factory production lines, can be rendered unanalyzable if leaked by utilizing secret sharing.
Nishimura: Indeed, in the age ahead, all information will be exchanged as data. Considering that, I feel EN technology has the potential to become indispensable as social infrastructure going forward.

●Implementation of ZEE within the Deloitte Tohmatsu Group
Nishimura: Could you tell us what specific solutions were provided for the implementation at Deloitte Tohmatsu Group this time?
Abe: This time, we have implemented ZEE ( EN Virtual Drive Enterprise Edition), the enterprise edition of ZVD ( EN Virtual Drive).
Nishimura: What was the scale of the provision?
Abe: This will be a deployment at the scale of tens of thousands of IDs. We will first implement a certain number and then proceed with phased expansion.
Nishimura: I see. So you're expanding while implementing upsells. Were there any particular points you focused on during the initial rollout?
Abe: While our company typically provides solutions to customers through sales agents, this time, since Deloitte Tohmatsu had already selected an infrastructure partner, our technical team provided direct support.
Nishimura: For such a large-scale implementation, didn't the adjustments require a significant amount of man-hours? How long did the implementation take?
Abe: Roughly about six months. We proceeded cautiously, conducting detailed checks for each usage scenario and repeatedly verifying compatibility with the application.
●Losing your PC ≠ Losing your data
Nishimura: I'd like to ask Mr. Noguchi a question now. When you first learned about ZenmuTech Inc.'s secret sharing technology, what potential solutions to challenges did you perceive?
Noguchi: Actually, I've been aware of ZenmuTech's technology for about ten years. Originally, in industries requiring high security, such as financial institutions, VDI (Virtual Desktop Infrastructure) and thin clients(※) were the mainstream solutions. Back then, VDI environments had limited capabilities compared to today, and streaming audio and video—especially for web conferencing—posed significant challenges. Consequently, "How can we achieve smooth operation in a thin client environment?" was a common concern shared by many companies.
※ VDI (Virtual Desktop Infrastructure) refers to a virtual desktop platform where users remotely connect to and utilize a virtual desktop environment built on servers. Thin clients are a system that uses terminals with minimal functionality, performing all processing on the server side, characterized by high security.
The primary reason VDI and thin clients were used in the first place was that "even if a device is lost, the data itself doesn't reside on the device, thereby avoiding the risk of information leakage." However, when we encountered ZenmuTech's technology, we sensed the potential for this fundamental concept to change. By leveraging secret sharing technology, we could ensure data security while running everything locally.This allows real-time applications like web conferencing to run smoothly and provides flexibility for future new solutions. The major appeal was that it maintained security while utilizing the local PC, rather than relying on the thin client mechanism.
The crucial point is that the concept of "data loss" fundamentally ceases to exist. Conventional encryption merely locks the data with a "key," meaning the data itself persists even if the device is lost.Therefore, regardless of whether it can be decrypted, the company cannot escape the fact that "data has been lost." However, with Zenmu Tech's secret sharing technology, the data is distributed. Thus, even if the device is lost, the data itself ceases to exist. In other words, the problem of "data loss" doesn't arise at all. This difference is extremely significant from the perspective of corporate information management, and I felt Zenmu Tech's technology holds tremendous potential.

● Cost reduction is possible without lowering security levels
Nishimura: I understand it's a highly effective solution for preventing data loss. Could you also tell me about ZEE's other strengths?
Noguchi: To reiterate, the most critical point is whether "protecting data" can be reliably achieved. What companies demand is "preventing data leaks." ZEE meets that requirement.ZEE maintains security levels equivalent to VDI while offering significant advantages in responsiveness and usability. From the user's perspective, ZEE's strength lies in its ability to prevent information leaks by invalidating data through this secret sharing technology. Even in the unlikely event of loss, information leaks are prevented.
● The secret to ease of use lies in mechanisms that don't rely on communication.
Nishimura: After implementation, what specific improvements in operational efficiency were observed?
Noguchi: I use it daily myself, and I feel the most significant improvement is the greatly enhanced stability of the response. In our previous environment using thin clients, delays in operation could occur depending on the network conditions. After introducing ZEE, we can now perform tasks smoothly with almost no impact from network conditions.
The mechanism of VDI and thin clients means that the actual data and processing occur on a remote server, so operations always require a network connection.For example, since keyboard input signals are sent to the server and the results are displayed on the screen, if the network is poor, you might experience phenomena like keystrokes appearing all at once several seconds later. Furthermore, when working outside the office using smartphone tethering, connection instability due to signal conditions can significantly impact operability.
However, ZEE fundamentally completes all processing locally on the PC, making it extremely low-dependency on communication.Unlike VDI or thin clients, which require "a certain level of network environment to function," ZEE's major strength is that it works perfectly well as long as it can synchronize the minimum necessary distributed data fragments. Consequently, its low communication load and minimal dependence on network conditions lead to a highly stable user experience.
Abe: I'm glad to hear you say that. Actually, this low communication load is also the result of technical ingenuity. EN, when distributing data, we keep each fragment to a very small size (about 1KB), which significantly reduces the load on the network.
Noguchi: I believe EN technology optimizes the balance between data protection and convenience while minimizing communication constraints, which contributes to its ease of use in the field.
Nishimura: For security personnel, the major appeal lies in the fact that it's "cost-effective, eliminates the risk of data leaks, and is secure." From the field perspective, the consistent performance even in unstable network conditions contributes to its ease of use. Regarding security, have you achieved the results anticipated before implementation? Have any unexpected issues arisen?
Noguchi: As far as actual usage goes, I haven't encountered any unexpected issues, and I believe we've achieved the expected level of security. I feel we've gained greater flexibility in performing our work while maintaining security equivalent to VDI or thin clients.

●Growth Strategy Based on Three Pillars
Nishimura: Now, let me ask about your future business development. While I see tremendous potential in your technology, I also recognize that management resources are limited, making a clear growth strategy essential. Could you share your direction for future business growth and your immediate goals?
Abe: We are currently developing our business around three core areas.
The first core area is PC data protection. We believe it is crucial to strengthen our sales partner network and expand not only in the Tokyo metropolitan area but nationwide.
The second pillar is OEM-based business expansion. Beyond PCs, our secret sharing technology can be applied to diverse fields like drones, security cameras, will management, and delivery company invoice management. We are actively expanding in this area, targeting not only the Japanese market but also overseas markets. We aim for further market growth by providing technology that enables data utilization while ensuring security.
The third pillar is the utilization of secure computation. Secure computation is a technology that enables analysis while keeping data confidential. For example, when multiple material manufacturers jointly develop new materials, analysis becomes possible without disclosing each company's confidential data. Crucially, even the research institutions handling the data cannot view its contents; only the final analysis results are fed back. We consider this not merely a security technology, but one that fundamentally transforms how data is utilized.Amidst the global challenge of "secure data circulation and utilization," particularly in Japan and the United States, EN confidential computation technology enables a system where data providers, recipients, and analysis institutions can all utilize only the necessary information without ever seeing the data itself.
We aim to accelerate our growth going forward, building upon these three pillars.
Nishimura: Thank you. I felt that the words you mentioned at the beginning—"data can become more free"—and the idea of "not just protecting data, but utilizing it" are precisely what connect to these initiatives. It really conveys that your company's mission is steadily taking shape.
●The Tokyo Consortium is the engine accelerating business
Nishimura: Finally, could you share a message for other startups considering joining the Tokyo Consortium?
Abe: As a startup, we constantly feel the challenge of not yet having fully established trust. Being selected for the Tokyo Consortium was a major turning point for us. Receiving support through the consortium gave us opportunities to connect with various companies. The companies introduced to us range widely—not just potential customers, but also alliance partners and valuable sources of feedback.
What stands out most is the "overwhelming difference in the quality of the first touch." Compared to conducting sales independently, engaging through the consortium program means meeting with partners who are genuinely prepared to listen seriously. When the initial contact is smooth, the subsequent pace of business development accelerates dramatically.
Furthermore, the tremendous passion and support from the consortium team, led by Mr. Nishimura, is a major draw.It feels less like simply receiving support and more like gaining an "extra engine" that accelerates our business. For companies like ours, which still lack sufficient name recognition, this program provides a major boost in building trust. I am convinced that this environment, where we can develop business with many companies while receiving such support, multiplies our growth speed many times over. I highly recommend this initiative to many startups.
Nishimura: Thank you. As the secretariat of the Tokyo Consortium, I personally consider it my mission to revitalize Japan through startup support. While your company's secret sharing technology may seem complex at first glance, it pioneers new possibilities in security through an innovative approach distinct from conventional cryptography. I firmly believe this unique concept, independent of encryption, will drive innovation across the industry. I sincerely wish you continued success in your future endeavors.

![[Interview] ZenmuTech Inc. × Deloitte Tohmatsu Financial Advisory LLC: Pioneering New Possibilities in Security with Secret Sharing Technology " EN " Main Visual](https://ecosystem.metro.tokyo.lg.jp/wp-content/uploads/2025/05/zenmu-top1.jpg)


